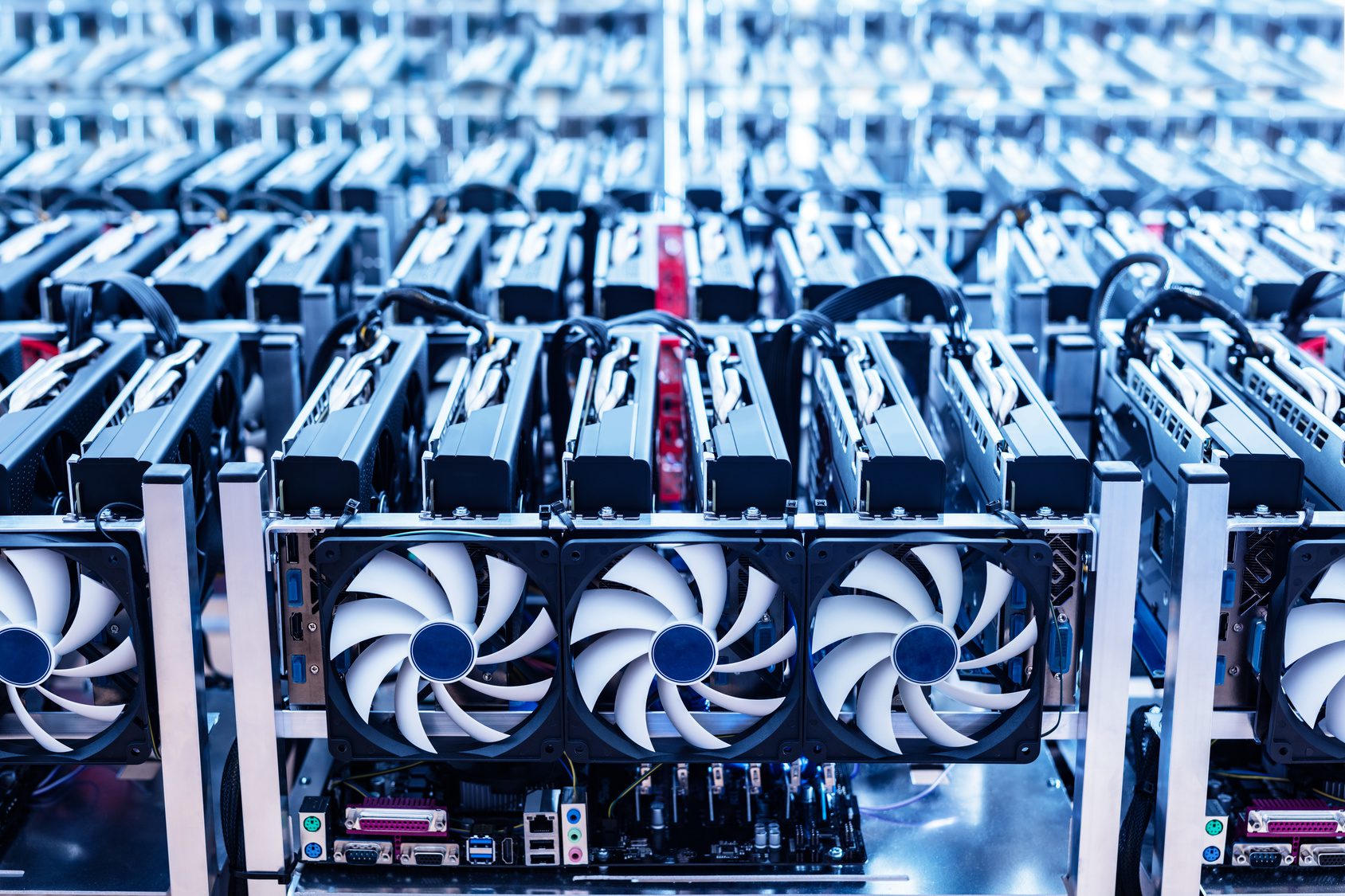
It almost seems quaint compared to ransomware, account takeovers, and data theft, but criminal miners are stealing processors wherever they can get them to improve their crypto mining success rate.
This is done using specialized Trojans and cloud services that offer free access for a period of time. Of course, these criminal miners may also ultimately just directly target crypto wallets:
“One risk comes from miners that attempt to abuse free resources on the internet provided by cloud and application service providers. Wang explained that what the miners might do is create many free accounts on these cloud infrastructures and get a good deal of computing power, at the expense of the service provider. She noted that such activity is considered to be against the terms of service, but the activity still needs to actually be identified so it can be stopped.
“Blocking crypto-mining activity, just like any detection work, is very much an arms race,” Wang said.
She noted that detecting indicators of crypto-mining activity can include conducting analysis of DNS traffic or monitoring for specific streams or patterns in network packets. As defenders are trying to identify the crypto-mining activity, she warned, the miners are also reacting to that activity and are working hard to avoid being detected.
Another risk Wang spoke about is cryptojacking.
“Miners are very resourceful, they’re very financially motivated, and some of them are attacking and compromising internet-facing computers to gain control of large numbers of resources to conduct mining activities,” Wang said.
Among the ways that cryptojacking is executed is with malware, such as WannaMine, which users are somehow tricked into installing by malicious sites.
Cryptocurrency Wallets Under Attack
Wang emphasized that the security pillars of confidentiality, integrity and availability all apply to cryptocurrency as well.
One of the key points of attack in the cryptocurrency world is what are known as cryptocurrency wallets. These are typically software-based vaults or “wallets” where users store the private cryptographic keys for the cryptocurrency they hold.
“If you get access to a cryptocurrency wallet, you effectively own the currency,” Wang said.
Attackers have been going after cryptocurrency wallets in different ways. One approach cited by Wang is with the ElectroRAT malware that is able to take over vulnerable wallets. ”
Overview by Tim Sloane, VP, Payments Innovation at Mercator Advisory Group