Criminals hacked their way into the Poly Network that enables users to swap tokens across multiple blockchains. Once into the Poly Network, the hacker used a vulnerability in smart contracts to steal from multiple blockchains stealing more than $600 million in various cryptocurrencies.
The reaction from the crypto community was swift and so far it appears the hackers have returned $258 million of the ill-gotten gains:
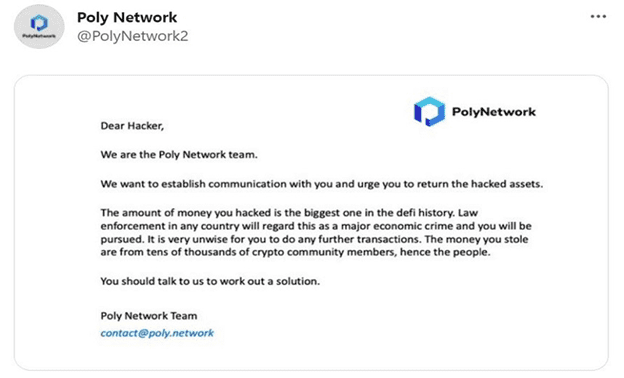
“In making its announcement, Poly Network tweeted: “We call on miners of affected blockchain and crypto exchanges to blacklist tokens coming from the [aforementioned] addresses.” The platform also wrote: “We will take legal actions and we urge the hackers to return the assets.”
In a follow-up post Tuesday addressed to the hacker, Poly Network wrote: “We urge you to return the hacked assets. The amount of money you hacked is the biggest one in the defi history.”
It continued: “Law enforcement in any country will regard this as a major economic crime and you will be pursued.”
Update
As of Wednesday, the Poly Network hacker had reportedly returned $258 million of the stolen funds, according to London-based blockchain analysis firm Elliptic.
Earlier Wednesday, Poly Network initially confirmed that the hacker had returned at least $4.8 million of the stolen assets.
The hacker’s return of funds “demonstrates that even if you can steal cryptoassets, laundering them and cashing out is extremely difficult, due to the transparency of the blockchain and the use of analytics,” says Tom Robinson, co-founder and chief scientist at Elliptic. “In this case, the hacker concluded that the safest option was just to return the stolen assets.”
According to the blockchain firm, the hacker has also posted a Q&A in an ethereum message, calling the Poly Network “a decent system” and “one of the most challenging attacks.” The hacker claims to have used a temporary and “untraceable” email and IP address.
A Poly Network spokesperson tells ISMG that “the hacker exploited a vulnerability, which is the _executeCrossChainTx function between contract calls. Therefore, the attacker uses this function to pass in carefully constructed data to modify the keeper of the EthCrossChainData contract.
“It is not the case that this event occurred due to the leakage of the keeper’s private key,” the spokesperson adds.”
Overview by Tim Sloane, VP, Payments Innovation at Mercator Advisory Group









