Podcast: Play in new window | Download
Fraud has been a persistent issue in the payments industry and has increased even more dramatically in recent years as it has shifted to predominantly digital channels. The total eradication of fraud is as unreachable a goal as the eradication of lying itself, but as fraudsters employ increasingly sophisticated measures to perpetrate their schemes, the payments industry must use its full arsenal of tools and strategies to mitigate risk, and prioritize strengthening authentication.
To learn more about the status and direction of fraud and its prevention, PaymentsJournal sat down with Matt Herren, Director of Payments Strategy at CSI, and Steve Murphy, Director of Commercial and Enterprise Payments Advisory Service at Mercator Advisory Group.
Fraud: a growing industry
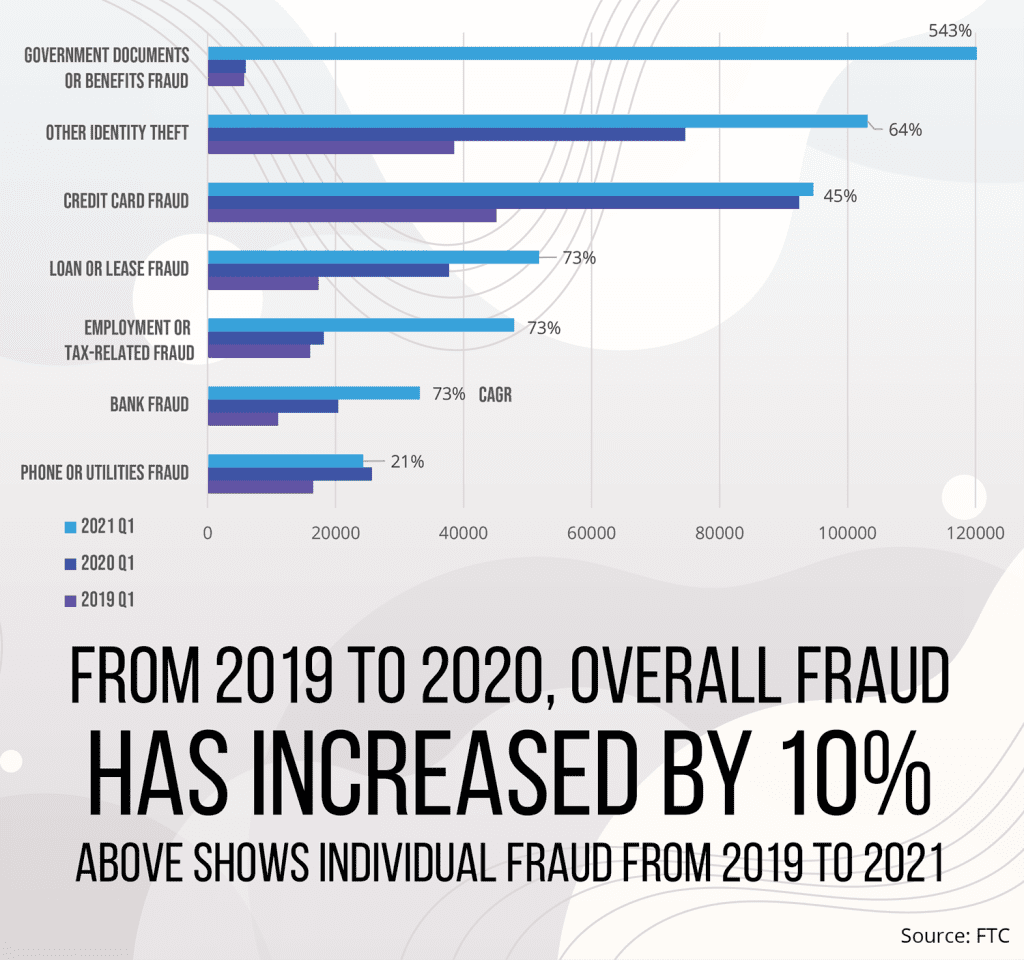
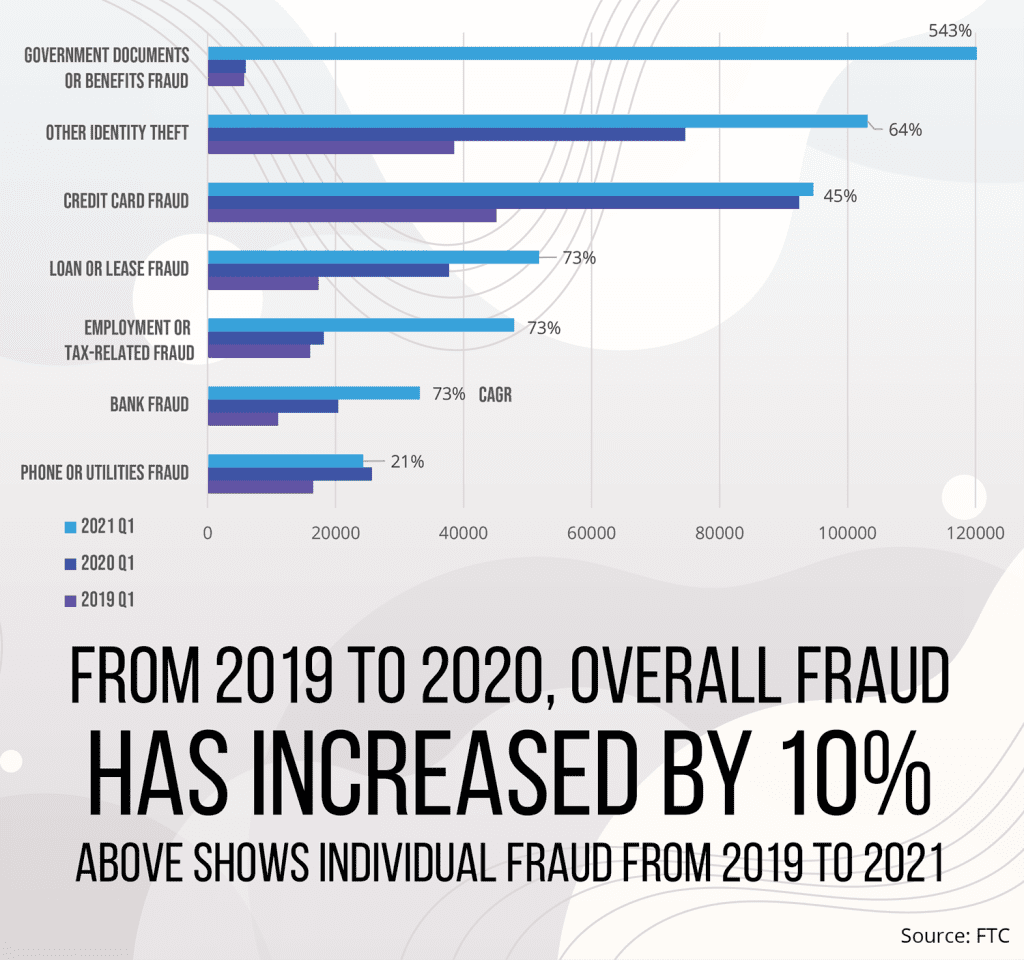
A 2020 Mercator consumer survey found fraud of all kinds, including bank, credit card, and lease/loan, increased by 10% from 2019, and this trend was corroborated by similar data from the FTC. The rapid shift to contactless and remote payments spurred by the COVID-19 pandemic is partially to blame, but the fact is that fraud has been rising steadily for years. “The sophistication of perpetrators outpacing institutional procedures, in my mind, is really the primary culprit,” said Herren.
Even more troubling is that “fraud as a service” has become an industry unto itself. Individual actors develop specialized skills such as data aggregation, social engineering, or security breaching, and offer those skills in the open market – almost like the various experts involved in a bank heist, but with better customer service. “We’re seeing the full-featured marketplaces take off,” warned Herren. “24/7 chat support, full warranty services with money bank guarantees, index search options by channels, geographic location, even specific institutions.” The organizational efficiency might almost be impressive if it wasn’t illegal, immoral, and robbing innocent people of their livelihoods.
Spear phishing, synthetic identity, and account takeover
Spear phishing, a form of phishing that focuses on high-value fraud targets rather than casting a wide net, has seen a particularly significant uptick. According to Herren, fraudsters are “using ancillary data from other breaches” to flesh out their strategies – i.e. incorporating insurance data, medical data, and other third-party vendor information to craft highly personalized phishing attacks. The victims of spear phishing are often those working in corporate upper management who conduct large-scale B2B transactions.
Fraudsters are also creating “synthetic identities” which are fake profiles cobbled together from real data. For example, a synthetic identity might use a real social security number but with the wrong name. “Social security number[s were] never really intended to be used as a piece of identity identification,” noted Herren, even though many companies request SSNs as a prerequisite for creating or verifying an account. Often the primary targets are young children whose credit reports, if they exist, are not usually closely monitored. “You steal Warren Buffet’s credit information, he’s probably going to be notified almost immediately,” said Herren. “But you steal [a] six-year-old’s information, the chances of successfully using personal information for fraudulent ends is much higher.”
Increasingly, spear phishing and synthetic identity fraud have been used not just to access one facet of personal information, but to control all parts of the fraud victim’s account from the inside out. “We’re really seeing a distinct shift from the lower-hanging fruit of stolen static card information toward more full account takeover,” Herren explained.
Preventative measures and best practices
Thankfully, there is technology is available that can make it much harder for cybercriminals to take advantage of private information. Armed with practical information, by following several simple steps coupled with the consultation of trusted partners such as CSI, you can establish serious roadblocks to fraudulent activity:
- Use EMV and Tokenization – This is one of the strongest methods for keeping card data protected. By moving away from static card information towards tokenization and cryptography, potential breaches will be less impactful and private information will be more secure.
- Test for Penetration – Testing security measures in a controlled environment is always preferable to waiting for a real attack to see if they work.
- Implement Fraud Recognition Training – People can be trained to be more mindful and cautious when sharing online information, not to click on third-party links in emails, and to recognize that most legitimate institutions will not request sensitive data by email in the way fraudsters do. Always call the real phone number of the institution to check.
- Vary Passwords – Make it a consistent practice to use different passwords for every account and change them regularly.
- Don’t Advertise Defenses – When banks post on their web sites about what kind of fraud defenses they use (such as blocking certain transaction types or regions), that information will be “scraped,” added to fraudsters’ profiles of potential targets, and used against them. Think of this as “Inverse Marketing.”
- Know That Criminals Are Persistent – If one channel for fraud is closed, fraudsters won’t suddenly decide to go straight and narrow; they just shift their energy elsewhere. Stay vigilant.
An ongoing project
There are no two ways about it: fraud is rampant, and our account information is vulnerable. “We have to embrace the reality that says if we give information out that can be stolen and subsequently used for fraud, it will be,” emphasized Herren. “Accept that, because the trends have perpetually shown that that’s the case.” The problem won’t disappear overnight, but the good news is that there are experts who can help level the playing field.
CSI has been exploring additional preventative measures including enhancing device biometrics, consortium data, and botnet screening. If banks stay ahead of the curve by working with CSI to adopt the latest fraud prevention strategies, they could become the trusted source for account validation, and could be compensated for doing so. “A few years ago, Ross Anderson, a professor of security engineering at Cambridge, said something that really stuck with me,” Herren concluded. “‘If you solve for authentication, everything else is just accounting.’ I think that’s a phenomenal way of thinking about it.”










