Tokenization is a one of kind data security strategy, known and adopted only by a few companies across the industry. One of the main reasons for the lack of adoption of this strategy is due to the misconception of considering tokenization and encryption to be the same. Unfortunately, people use the two terms interchangeably and haven not recognized the true power of tokenization. However, in today’s article, I hope to dispel the myth and help people understand what is tokenization? And why is it considered one of the best security strategies for credit card data and Payment Card Industry Data Security Standard (PCI DSS) scope reduction?
What is Tokenization?
Tokenization is a process of replacing sensitive data elements, with a non-sensitive element, known as a token. One of the best examples of this could be replacing a bank account number or card number with random characters or elements that have no essential or exploitable value. It is a process that retains all the pertinent data without compromising its security. So, in the case of the tokenization system, it does not decipher the token and reveals the sensitive data. This process is very different from encryption which allows data to be deciphered using a secret key.
How does Tokenization work?
Tokenization in relation to credit card payment processing involves replacing of sensitive credit card or account number with a token. A token is nothing but alphanumeric ID having no exploitable value or meaning or connection to the 16 digits primary account number (PAN) of the customer. This is typically done to remove any connection between the transaction and the sensitive data, this limits the risk of a breach of sensitive data. Tokenization of data safeguards credit card numbers and bank account numbers in a virtual vault, for organizations to safely transmit data especially via wireless networks. For tokenization to be effective, organizations must use a payment gateway to safely store sensitive data. A payment gateway is a service offered by an e-commerce application service provider that facilitates/permits direct payments or credit card processing. This gateway stores credit card numbers securely and generates the random token.
Example of How Tokenization works
For example, when a merchant processes the credit card of a customer, the PAN 1234-5627-8910-1112 is replaced with a token 68@y%lk268tgsc. Hereafter the merchant applies a token ID to retain records of the customer, for example, 68@y%lk268tgsc is Tom Holland’s PAN details. The token is then transferred to the payment processor who de-tokenizes the ID and confirms the payment. Only the payment processor can de-tokenize the 68@y%lk268tgsc to its original PAN 1234-5627-8910-1112and process the payment.
In the credit card payment process, the payment tokens are automatically issued on a real-time basis and used online in predefined domains or payment environment. In a tokenized payment process, the PAN is not transmitted during the transaction, thus ensuring the payment process to be secure. So, with tokenization the PAN is never compromised and which is why there is very little possibility of data theft, breach, or any fraudulent activity, even if the payment tokens are accessed by a hacker.
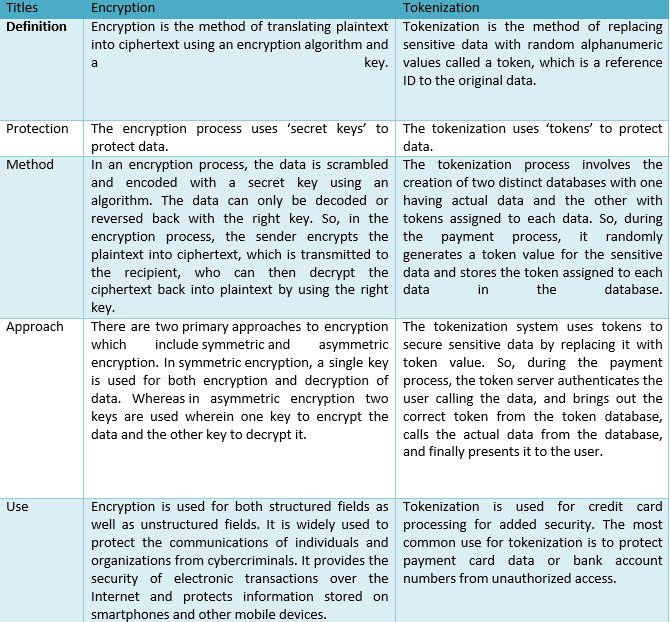
Difference between Tokenization & Encryption
How does tokenization help reduce the PCI DSS scope?
Most online businesses today handle sensitive business-critical data of their customers and so they look for ways to limit their PCI scope. Reducing the PCI DSS Scope meansreducing the cost, effort, and risk that comes with PCI compliance. After all, the less CHD your organization holds, the less you will have to convince your Qualified Security Assessor (QSA) that you are doing everything you can to protect consumer data. To bolster this effort organizations have started adopting the Tokenization Strategy to reduce the scope of PCI DSS Compliance.
As we all know,Tokenization eliminates the need of storing CHD in your environment. Tokenization helps companies achieve PCI DSS compliance by reducing the amount of PAN data stored in-house. Instead of storing sensitive cardholder data, the organization only handles tokens, thus reducing the data footprint in your environment or in some cases, becoming even totally out of scope of the PCI DSS requirements. Less sensitive data translates into significantly lesser compliance requirements to comply with, and this may further facilitate the quicker audit process. This automatically reduces your efforts to protect the critical data from theft or breach. However, in this scenario, it is critical to ensure the payment processors you collaborate with are compliant to PCI DSS standard and efficiently secure data.
Although adopting the tokenization strategy significantly reduces your PCI DSS Compliance scope, it is, however, still your responsibility to ensure the vendor you choose to collaborate with is safeguarding your customer’s data.Ensure your tokenization vendor is approved, protects the tokenization systems and processes with strong security controls. However, it is important to note that with PCI DSS, , “Tokenization solutions do not eliminate the need to maintain and validate PCI DSS compliance, but they rather simplify the validation efforts by reducing the number of system components for which PCI DSS requirements apply”. Having said that, the extent to which tokenization reduces a company’s scope completely depends on how a company’s technology and business processes interact with payment card data.
Conclusion – Is the tokenization recommended for your organization?
Any business environment handling sensitive data should ideally use tokenization to reduce risk and secure data. But it is equally essential for businesses to carefully evaluate a provider before collaborating with them and directly jumping headfirst into the tokenization strategy. Businesses are suggested to first perform a thorough risk assessment when selecting a tokenization service provider to ensure they are contracting with a secure entity. So, before you move ahead with this strategy, make sure the service provider is PCI DSS compliant, and ensure you follow up with them every year to verify their compliance status from time to time.
Narendra Sahoo (PCI QSA, PCI QPA, CISSP, CISA, CRISC) is the Founder and Director of VISTA InfoSec.









